Web Security for Web Artisans
ASAWL turns Laravel security guidance into a structured reading path with practical vulnerabilities, tutorials, and review habits you can apply to real projects.
Bilingual reference
English and Spanish documentation from the same source.
Laravel-first
Framework-specific guidance instead of generic web advice.
Review-ready
Useful for workshops, audits, and day-to-day engineering reviews.
Jorge Pullas
ASAWL Author
Build secure Laravel systems with the same care you use to build elegant ones.
- Threat modeling through Laravel features
- Common vulnerability patterns and mitigations
- Operational hardening for teams and deployments
Web Application Security Analysis for Laravel (ASAWL)
Within the scope of web application security analysis developed in the context of this repository, ASAWL is a methodology designed to assess and improve the security of web applications built with Laravel. Its main focus is the identification and mitigation of Vulnerabilities by applying security best practices specific to this ecosystem.
Laravel, thanks to its power and popularity, enables agile development of robust web applications using PHP. However, like any tool, using it does not automatically guarantee security. ASAWL arises from the need to address this reality by providing a structured and practical framework to evaluate application security.
Blog Example (How To Read The Docs)
All vulnerability pages in this site use the same example domain: a simple blog with Post and Comment.
Rules used across the examples:
- Anyone (including guests) can read posts and comments.
- Any authenticated user can write a comment on any post.
- Only authorized users can create/update posts (example:
is_author; optionalis_admin).
Where the example code lives:
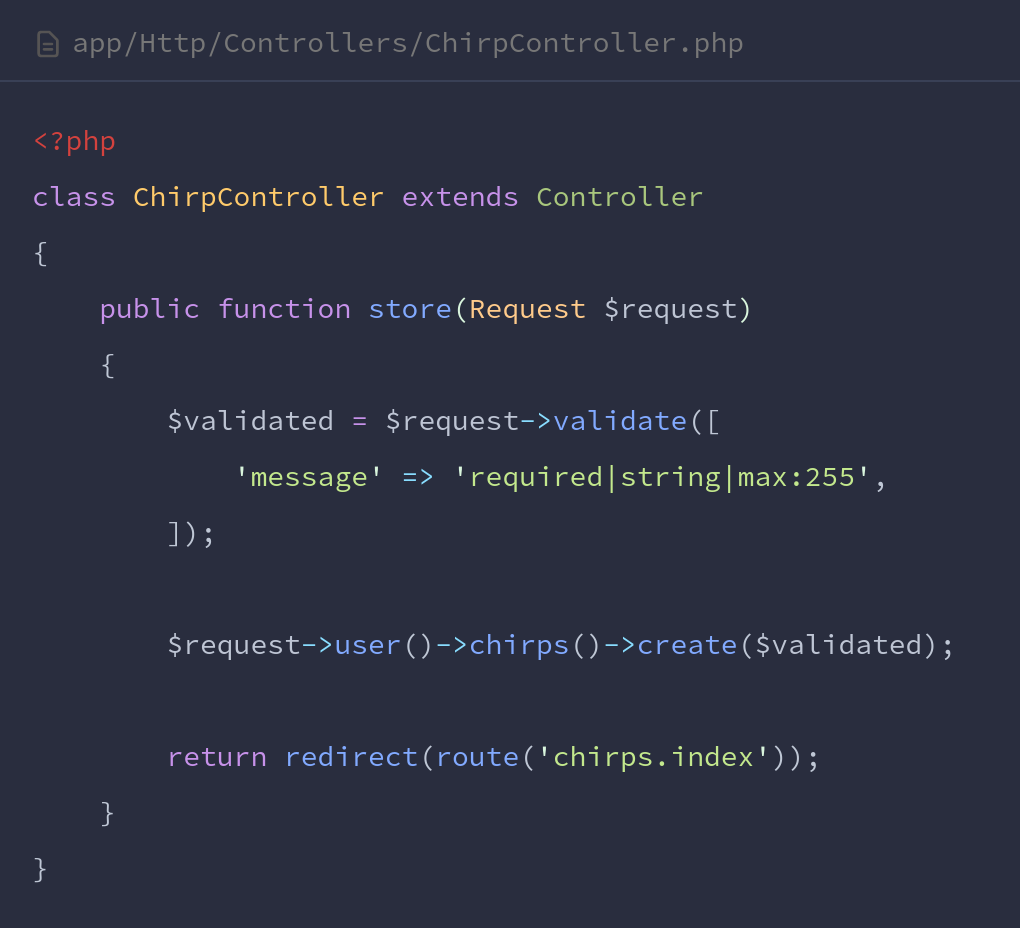
app/Example/**(Actions, Policies, Requests, Controllers)
How it is applied in Documentation / Vulnerabilities:
- Each A01-A10 page explains the risk and then shows the secure implementation for the blog rules.
- Snippets reference real files in this repository so you can trace the fix from documentation to code.
- When a fix is configuration-related (A02, A09, A10), the snippet points to the exact
config/*orbootstrap/app.phpsurface.
Vulnerabilities
- A01: Broken Access Control
- A02: Security Misconfiguration
- A03: Software Supply Chain Failures
- A04: Cryptographic Failures
- A05: Injection
- A06: Insecure Design
- A07: Authentication Failures
- A08: Software or Data Integrity Failures
- A09: Security Logging and Alerting Failures
- A10: Mishandling of Exceptional Conditions